Your storage room is full again. Retired laptops, dead monitors, a few old switches, maybe a stack of drives nobody wants to touch because nobody wants the liability. That’s usually when someone types e-waste recycling near me into Google and assumes the closest option is good enough.
For a business, that’s a mistake.
Local convenience matters far less than documented control, certified data destruction, and liability transfer. If a vendor can’t prove where your assets went, who handled them, and how data was destroyed, you’re not recycling responsibly. You’re outsourcing risk badly.
The Hidden Risks in Your 'E-Waste Recycling Near Me' Search
Most “near me” results are built for convenience, not commercial compliance. That’s fine for a household dropping off a broken toaster. It’s not fine for an IT manager disposing of laptops, servers, phones, copiers, or storage media that may still contain regulated data.

The broader waste stream shows why this matters. Global e-waste reached 53.6 million metric tons in 2019, and only 17.4% was formally collected and recycled, leaving over 80% unmanaged and vulnerable to improper handling, according to the Global E-waste Monitor. When your retired devices enter that unmanaged gap, your company keeps the exposure.
Convenience is not compliance
A local drop-off site might accept electronics. That doesn’t mean it provides:
- A chain of custody from pickup through final processing
- Certified data destruction aligned with recognized standards
- Asset-level reporting for audits and internal records
- Downstream accountability for where material goes
If those controls are missing, your disposal process is weak at the exact point regulators, auditors, and legal teams care about most.
Practical rule: If a recycler can’t document custody from your office to final disposition, don’t hand over data-bearing devices.
The real business risk
The common failure isn’t dramatic. It’s ordinary. A closet cleanup turns into a rushed handoff. Someone loads equipment into a van. No serialized inventory is created. No destruction certificate follows. Months later, you can’t prove what happened to the drives.
That’s why certified standards matter. If you need a baseline for what responsible processing looks like, review R2 certification requirements for electronics recycling. A business disposal program should be defensible on paper, not just convenient in practice.
The phrase e-waste recycling near me sounds local and harmless. For companies, it often hides a bad assumption: that physical proximity equals safe disposition. It doesn’t. A nearby uncertified outlet can create more legal, financial, and reputational risk than a managed provider operating a longer route with documented controls.
Evaluating Providers Beyond Proximity and Price
Price gets too much attention. The better question is simpler: which vendor is willing to absorb operational responsibility and prove it?
Uncertified municipal drop-off centers offer no certified data destruction or chain-of-custody documentation, exposing organizations to FTC Disposal Rule violations with fines up to $50,120 per violation, while certified ITAD firms provide auditable proof of compliance, as noted by Keep Smyrna Beautiful’s recycling guidance.
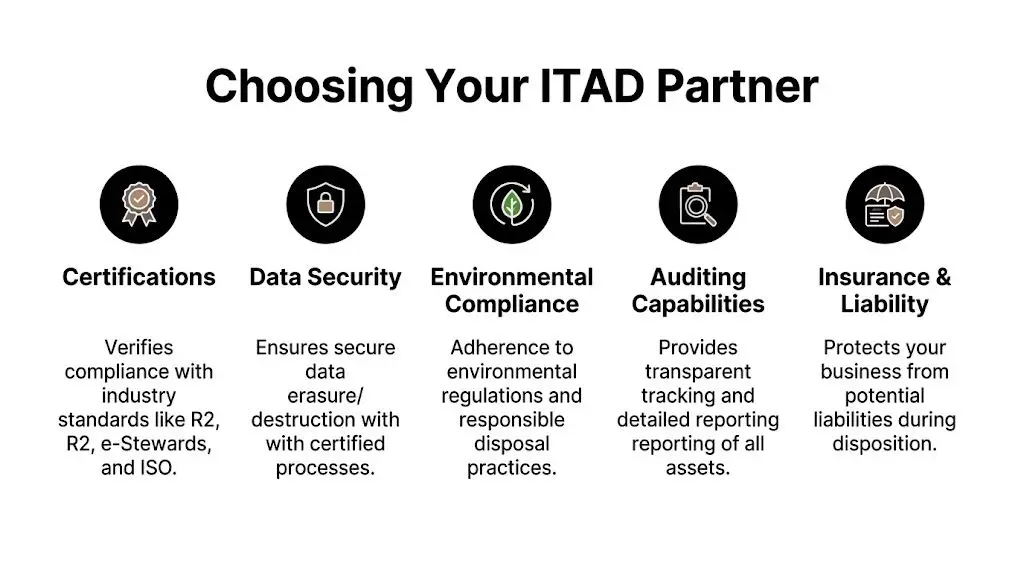
What to verify before you sign anything
Use this as a screening list, not a wishlist.
- Certifications that mean something. Ask whether the provider operates under recognized electronics recycling and process controls. If they mention R2v3, e-Stewards, or RIOS, ask what those certifications cover in their operation.
- Data destruction method. Some assets should be wiped. Others should be shredded. The vendor should explain when it uses software sanitization under NIST 800-88 practices and when physical destruction is the better choice.
- Audit trail. You need asset-level inventory, custody records, and final documentation that your compliance team can store.
- Insurance. Ask for proof of relevant coverage, especially around pollution liability and data-related exposure.
- Downstream transparency. If they ship material elsewhere, ask who receives it and whether those downstream partners are also controlled.
Ask direct questions
A good vendor won’t resist these.
| Question | What a solid answer sounds like |
|---|---|
| How do you track assets? | Serialized inventory, asset tags, scanned handoff records |
| How is data destroyed? | Documented wiping or shredding, with reporting |
| What paperwork do I receive? | Certificates plus detailed asset and processing reports |
| What happens downstream? | Named process controls, documented partners, no vague answers |
If the sales rep keeps steering you back to “free pickup,” you’re talking to a hauler, not a risk-management partner.
One practical option is to run vendors through a formal checklist before approving any pickup. A vendor due diligence checklist for ITAD and recycling partners helps force the conversation into controls, documentation, and accountability instead of marketing claims.
The cheapest quote is often the worst one
Low bids usually strip out the expensive parts of doing the work correctly. Those parts include secure handling, reporting, proper downstream controls, and enough operational discipline to survive an audit.
If your company is in healthcare, finance, education, government, or any environment with regulated data, don’t choose a recycler the way you’d choose office furniture removal. You’re not paying for disposal alone. You’re paying for a documented process that protects your organization after the equipment leaves your site.
Preparing Your IT Assets for Secure Disposition
Internal sloppiness ruins otherwise good recycling projects. Before any truck arrives, fix your side of the process.
In a Stanford analysis, 40% of enterprises cited data privacy fears as a primary reason for hoarding old equipment, and barcode or RFID-based auditing provides 100% inventory traceability, according to this review of barriers to e-waste recycling and chain-of-custody controls. That fear is rational. The fix is process.
Build the inventory before pickup day
Start with a real asset register, not a rough count.
- List each device by type. Laptop, desktop, server, firewall, switch, printer, copier, mobile device, external drive.
- Capture serial numbers and internal asset tags. If you can’t match what left the building to what was processed, your records are weak.
- Flag data-bearing equipment. Drives, backup devices, phones, multifunction printers, and certain medical or lab systems need tighter handling.
- Mark likely reuse candidates. Newer business hardware may have resale value. Dead or obsolete units may need destruction and commodity recycling.
Control access while assets wait
Too many companies pile retired equipment in unsecured rooms, loading docks, or storage containers. If you stage equipment before pickup, treat it like controlled property. Restricted access, sign-in logs, and tamper awareness matter. If you use containers or temporary outdoor storage, this UK shipping container security guide is a useful reference for physical safeguards that reduce opportunistic theft and unauthorized access.
The chain of custody starts before the recycler arrives. Your internal staging process is part of the evidence trail.
Match disposition to asset condition
Not every device should follow the same path.
- Functional, newer equipment may belong in remarketing or IT asset recovery.
- Broken but data-bearing hardware usually needs immediate sanitization or shredding.
- Specialized devices such as medical, lab, or industrial systems need review for embedded storage and regulated components.
If your team needs a benchmark for sanitization practices, use NIST SP 800-88 guidance for media sanitization as the baseline standard when discussing wiping versus destruction with vendors.
Good preparation does two things at once. It lowers compliance risk, and it gives you a better shot at value recovery on assets that still have market life.
Understanding Logistics Costs and Final Documentation
The phrase “free pickup” causes more bad decisions than almost any other term in this market.
Many “free” e-waste pickup services have hidden qualifiers, including minimums of 200+ lbs, and often exclude certified data wiping, which can add $0.50 to $2.00 per pound, according to this review of electronics recycling pickup requirements and service exclusions. For businesses, “free” often means the vendor is free to bill later for the parts that protect you.
What drives cost
Logistics pricing usually depends on a mix of factors:
- Volume and palletization. A few loose devices cost more to handle than organized bulk loads.
- Type of equipment. Servers, rack gear, batteries, copiers, and specialty devices take more labor.
- On-site services. Shredding, de-installation, packing, and scanning add work but also add control.
- Distance and routing. Managed transport isn’t just a freight issue. It’s a custody issue.
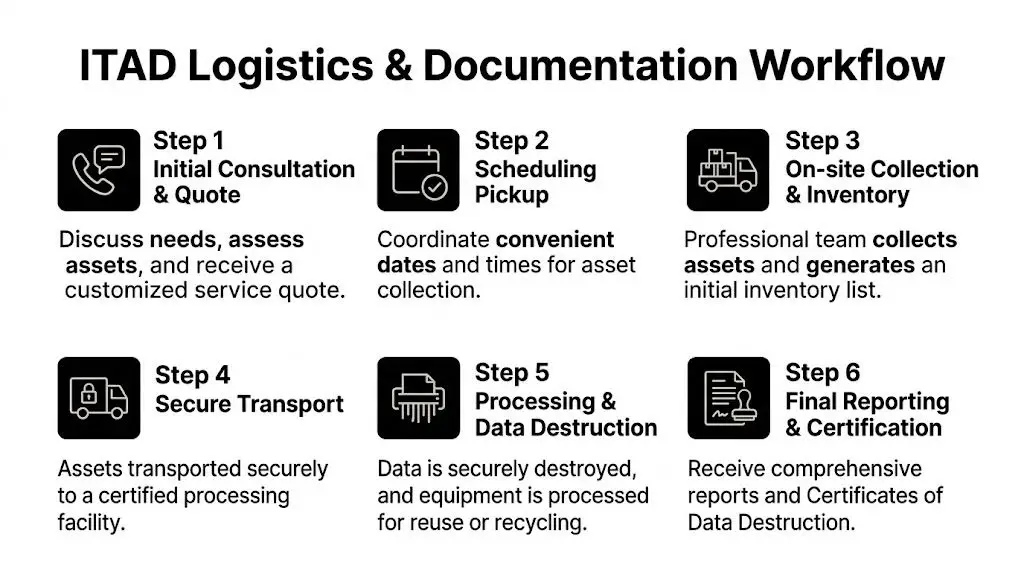
A business should prefer a managed pickup over casual drop-off for one reason. With a proper logistics chain, there’s documentation from handoff through processing.
Don’t close the project without the paperwork
You need final records that hold up in an audit, an internal compliance review, or a legal dispute.
Look for two core documents:
| Document | Why it matters |
|---|---|
| Certificate of Data Destruction | Shows data-bearing assets were sanitized or destroyed through a documented method |
| Certificate of Recycling | Shows equipment was processed through an accountable recycling stream |
Ask for supporting detail, not just a generic certificate. Asset lists, serial references, processing dates, and method descriptions make the document useful.
A certificate without traceable asset detail is better than nothing, but not by much.
If you want to see what adequate documentation should include, review a destruction certificate template for IT asset disposition records. It helps procurement, compliance, and IT align on what they should demand before approving any vendor.
One provider that offers nationwide pickup, data destruction, and documentation for organizations is Beyond Surplus. That matters less as a brand point than as an operational model. For business e-waste recycling near me, a managed chain beats a nearby unknown every time.
Answering Your Top Business E-Waste Questions
Is e-waste recycling the same as ITAD
No. Basic recycling focuses on material disposal. IT asset disposition focuses on security, documentation, and value recovery first, then responsible recycling for what can’t be reused.
Certified enterprise ITAD programs can reach 85-95% material recovery, with 99.9% secure data sanitization via on-site shredding, while 70% of e-waste lacks chain-of-custody documentation in informal channels, according to this analysis of enterprise ITAD recovery and data sanitization practices. That gap is the difference between a managed process and a gamble.
Can my company get money back for old equipment
Sometimes, yes. Business-grade laptops, servers, networking gear, and late-model devices may still have resale value. But don’t let the possibility of buyback distract from the main objective. If a vendor talks aggressively about resale and vaguely about data destruction, your priorities are misaligned.
The right order is simple. Secure the data. Document the custody. Then recover value where it’s justified.
How do we stay compliant in regulated industries
Use a provider that can produce auditable records, destruction documentation, and asset-level reporting. Your legal and compliance teams need proof, not assurances. That’s especially true for healthcare, finance, education, and government environments where one sloppy disposal event can create lasting problems.
What about specialized equipment
Treat medical devices, lab equipment, and data center hardware as higher-risk categories. They often involve embedded storage, unusual components, or more complicated removal. A general scrap operator usually isn’t equipped for that work.
For a broader view of commercial services, review business e-waste and IT equipment disposition options.
If you’re sorting through old IT equipment and want a disposal process that prioritizes chain of custody, certified data destruction, compliant recycling, and usable documentation, contact Beyond Surplus.