Think for a moment: every retired hard drive in your business's storage room is a filing cabinet packed with your company’s most sensitive information. It contains everything from proprietary financial records and client data to private executive communications.
Secure hard drive destruction isn't just another item on an IT manager's checklist. It is an essential component of a comprehensive risk management strategy. The objective is to permanently and irreversibly destroy data on end-of-life hard drives, ensuring it can never be recovered by any means.
Why Secure Hard Drive Destruction Is Not Optional
Simply tossing an old hard drive into a dumpster is the corporate equivalent of leaving your company's vault key on a public bench—a catastrophic and unnecessary risk. For any business, from a local enterprise to a national corporation, improper disposal is a direct invitation to crippling data breaches, severe damage to your brand’s reputation, and massive financial penalties under regulations like the FTC Disposal Rule and HIPAA.
In today's data-driven economy, professional data destruction is a non-negotiable part of corporate governance and risk management. It is a mandatory business practice.
The market reflects this urgency. The Data Destruction Service Market was valued at USD 12 billion in 2025 and is expected to hit USD 13.5 billion in 2026. This growth is fueled by the sheer volume of information we're creating—global data creation reached a mind-boggling 181 zettabytes in 2025. The cost of getting it wrong is also skyrocketing, with data breaches costing companies an average of $4.88 million per incident in 2024.
The Real-World Consequences of Negligence
Failing to properly destroy data carries tangible risks that extend far beyond a single lost file. The consequences can impact every facet of your organization.
- Crippling Financial Penalties: Regulatory bodies enforce data protection laws stringently. HIPAA violations, for example, can result in fines reaching millions of dollars for a single incident involving unprotected patient information.
- Irreparable Brand Damage: A public data breach can shatter customer trust and loyalty in an instant. Rebuilding a brand's reputation after such a failure is a long, expensive, and often futile endeavor.
- Legal Liability: Your business has a legal and ethical duty to protect the sensitive information it collects. Failure to do so can lead to lawsuits from clients, business partners, and employees whose data was compromised.
Integrating Destruction into Your Security Strategy
A robust security plan must encompass the entire lifecycle of your data, not just its period of active use. Strong Data Loss Prevention (DLP) strategies must include the end-of-life phase for all storage media to prevent these types of costly and preventable breaches.
This means every single hard drive, whether from a large-scale data center server or a C-level executive's laptop, requires a documented and certified destruction plan.
Your company's data lifecycle doesn't end when a hard drive is unplugged. True security demands that the data's final moments are managed with the same rigor as its active use, ensuring complete and permanent erasure.
Understanding your options—from physical shredding to certified data erasure—is the first step toward safeguarding your company’s future. Partnering with a certified ITAD provider like Beyond Surplus ensures this critical process is handled professionally, compliantly, and with the necessary documentation to satisfy any audit.
Comparing Hard Drive Destruction Methods
You have a collection of retired hard drives. What is the next step? Choosing the correct method to destroy the data they contain is a more significant decision than many businesses realize. Not every method offers the same level of security, and the optimal choice depends on your specific security requirements, budget, and any potential for hardware reuse.
Understanding the primary differences will enable you to make an informed decision that protects your sensitive corporate information. The options can be categorized into three main approaches: physical destruction (shredding), magnetic destruction (degaussing), and software-based destruction (data wiping).
Physical Destruction with Hard Drive Shredding
Hard drive shredding is precisely what it sounds like—and it is the most direct and visually verifiable method of data destruction. Imagine an industrial-strength version of an office paper shredder, engineered to tear through steel, aluminum, and plastic. A specialized shredding machine utilizes powerful, interlocking blades to grind a hard drive and its internal platters into small, confetti-like metal fragments.
Once a drive passes through a shredder, the data is permanently gone. There is zero possibility of reassembling the fragments to recover any information. This absolute certainty is why shredding is the preferred method for government agencies, healthcare organizations, and any enterprise that cannot afford to take any risks with its data.
The primary advantages of shredding are clear:
- Irreversible Destruction: This provides the highest level of data security possible. By physically obliterating the storage media, data recovery becomes impossible.
- Compliance Certainty: Shredding meets the requirements of the most stringent data privacy regulations, including HIPAA, FACTA, and the DoD 5220.22-M "Destroy" standard.
- Clear Verification: You can physically observe the pile of destroyed drives. It provides undeniable proof of secure disposal.
The only significant drawback is that the drive is completely destroyed. This means it cannot be resold to recover value, and it generates electronic waste that must be managed and recycled responsibly.
Ignoring proper destruction carries major risks, from data breaches and hefty fines to serious brand damage.
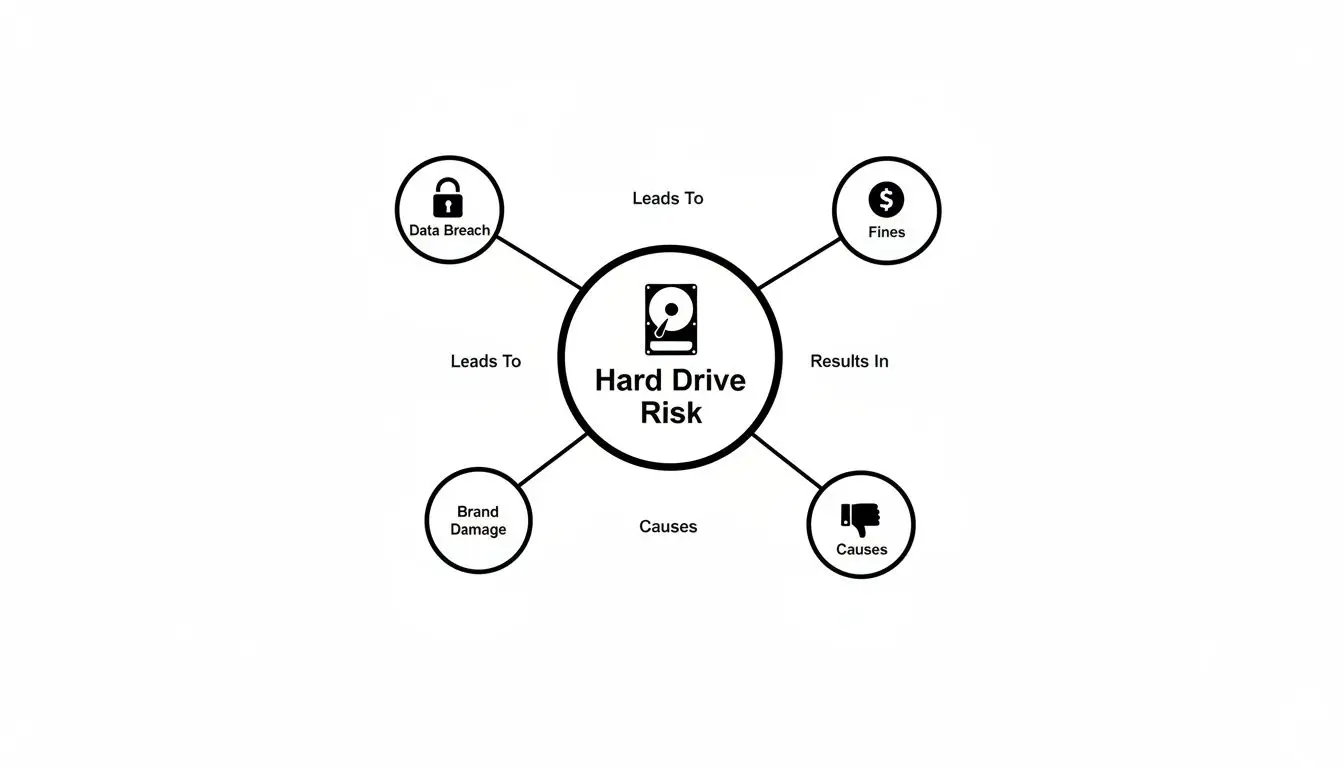
This is a stark reminder of why a guaranteed destruction method is so crucial for managing risk.
Magnetic Destruction with Degaussing
Degaussing is another method of physical destruction that uses powerful magnetic forces instead of mechanical shredding. A degausser subjects the hard drive to a magnetic field far more powerful than the one the drive uses to store data.
This process completely scrambles and neutralizes the magnetic signature on the drive's platters, effectively turning organized data into an unreadable, chaotic mess. The drive is rendered inoperable, and the data is permanently erased.
CRITICAL NOTE: Degaussing is highly effective for traditional magnetic hard disk drives (HDDs). However, it is completely ineffective on Solid-State Drives (SSDs), which use flash memory chips and do not rely on magnetism for data storage.
To learn more about the technology, you can explore what degaussing is in our detailed guide. Like shredding, a degaussed drive is rendered useless, so there is no opportunity for reuse or resale.
Logical Destruction with Data Wiping
Data wiping, also known as sanitization, employs a different strategy. Instead of physically destroying the drive, this software-based method overwrites every bit of existing data with random binary code—typically a pattern of zeros and ones. This is performed multiple times in several passes to ensure the original information is buried and completely unrecoverable.
The process is analogous to taking a book and methodically writing gibberish over every single word until no trace of the original text remains.
The primary advantage is that the hard drive remains fully functional. It can be reused, refurbished, or resold, which supports corporate sustainability goals and can generate a return on investment (ROI).
To clarify the choice, here’s a quick comparison of these methods.
Comparison of Hard Drive Destruction Methods
| Method | Security Level | Compliance Suitability | Drive Reusability | Typical Use Case |
| :— | :— | :— | :— |
| Physical Shredding | Very High | Highest Level (HIPAA, DoD) | None | End-of-life media, top-secret data, maximum security needs. |
| Degaussing | Very High | High (for HDDs) | None | Quick and secure erasure of magnetic hard drives (HDDs). |
| Data Wiping | High | High (NIST 800-88 Purge) | Yes | Asset remarketing, value recovery, supporting sustainability goals. |
Data wiping is fully compliant with standards like NIST 800-88 "Purge," making it a secure and reliable choice for most businesses. The trade-off is time. Wiping can be a slow process, particularly with large batches of high-capacity drives, and it requires careful auditing to verify that every sector was successfully overwritten.
Navigating Data Destruction Compliance Regulations
For most commercial organizations, the secure disposal of retired hard drives is not merely a best practice—it is a legal mandate. Failure to comply with data disposal laws can lead to staggering fines, legal action, and a complete erosion of customer trust. Understanding this complex regulatory landscape is the first step toward creating an ironclad, audit-proof data destruction policy for your business.
These regulations carry significant real-world consequences. A healthcare provider, for example, must ensure the physical destruction of hard drives containing Protected Health Information (PHI) to comply with HIPAA. Similarly, a financial services firm managing consumer data is bound by the Gramm-Leach-Bliley Act (GLBA), which mandates secure disposal to protect customer privacy.
Understanding Key Destruction Standards
In the United States, the most critical standard is the NIST Special Publication 800-88. This document from the National Institute of Standards and Technology provides clear guidelines for sanitizing digital media and serves as the go-to framework for most industries and auditors.
NIST defines three distinct levels of sanitization:
- Clear: A basic overwrite using standard read/write commands. It is sufficient to prevent simple data recovery but may not withstand a determined forensic analysis.
- Purge: A more advanced method using specialized software overwriting or degaussing to make data recovery practically impossible. A purged drive can be safely reused within an organization.
- Destroy: The final level of data sanitization. It involves physically destroying the media through methods like shredding, pulverizing, or incineration, from which there is no recovery.
The choice between these methods depends on the sensitivity of your data and your company's risk tolerance. For a deeper analysis of these standards, consult our detailed guide on NIST SP 800-88.
The Certificate of Destruction: Your Proof of Compliance
How do you prove compliance when an auditor arrives? The answer is a Certificate of Destruction. This formal document, provided by a certified ITAD partner like Beyond Surplus, serves as the official record that your assets were destroyed in a compliant manner.
A Certificate of Destruction is more than a receipt; it is a legal document that formally transfers liability. It provides concrete evidence of your due diligence, protecting your organization from claims of negligence.
This legal proof is absolutely vital. It demonstrates that you took deliberate, professional steps to protect sensitive information at the end of its lifecycle. If your data handling practices are ever questioned, this documentation is your primary defense.
Market Growth and Regulatory Pressure
Increasing regulatory pressure is a major driver behind the high demand for professional destruction services. North America leads the Hard Drive Shredding Services Market, valued at USD 0.72 billion in 2024 and projected to reach USD 1.27 billion by 2035.
This growth is largely a response to the vast quantities of electronic waste from data centers and technology companies, all of which are governed by privacy laws like HIPAA and CCPA. As these regulations become even stricter, the need for certified, verifiable destruction services will only escalate. You can read more about these market trends and their drivers.
Ultimately, navigating compliance is not about memorizing every law. It is about implementing a solid, documented process for the secure destruction of hard drives and partnering with a vendor who provides the certification you need to prove it.
Choosing Between On-Site and Off-Site Destruction

Once you have determined how you will destroy your old hard drives—whether by shredding, degaussing, or wiping—the next critical question is where. Your two primary options are on-site destruction, which occurs at your business location, and off-site destruction, where your assets are transported to a secure facility.
Each approach offers distinct advantages. The best choice depends on your company's security policies, budget, and operational needs.
Consider this analogy: on-site destruction is like hiring a private chef to cook in your kitchen, where you can oversee every step. Off-site destruction is like ordering from a high-security, top-rated commercial kitchen known for its impeccable standards and efficiency. Both deliver a premium result, but the experience and oversight differ entirely.
The Case for On-Site Hard Drive Destruction
On-site, or mobile, destruction provides the highest level of security and complete peace of mind. A specialized truck equipped with industrial-grade shredding machinery arrives at your location. Your staff can witness the entire process, from scanning serial numbers to the final destruction of the drives.
This method establishes an unbroken chain of custody. Since the data-bearing drives never leave your premises before being destroyed, it is the preferred choice for organizations with the strictest security requirements.
Key benefits of on-site service include:
- Maximum Security: Your data-bearing assets are destroyed before they ever leave your sight, completely eliminating any transportation-related risks.
- Total Transparency: You can witness the destruction in real-time, providing undeniable proof that the job was completed correctly.
- Immediate Verification: The process is completed on the spot, and you receive your documentation, including a Certificate of Destruction, immediately.
This level of assurance is why government agencies, healthcare organizations, and financial institutions frequently mandate on-site services. It provides a definitive, tangible answer when auditors inquire about your protocol for the secure destruction of hard drives.
The Case for Off-Site Hard Drive Destruction
Off-site destruction is a highly efficient and cost-effective option, particularly for businesses dealing with a large volume of IT assets. With this service, a certified ITAD partner picks up your hard drives in securely locked containers and transports them in GPS-tracked vehicles to a specialized, access-controlled facility.
These processing plants are designed for high-volume operations and are subject to rigorous, continuous security audits. Although you do not witness the destruction firsthand, you receive the same detailed, serialized Certificate of Destruction upon completion, confirming your assets were disposed of securely and in full compliance with all regulations.
Off-site destruction leverages economies of scale to offer a more affordable price point without compromising on security. The entire process occurs within a controlled environment specifically designed for this purpose.
Advantages of choosing off-site destruction include:
- Cost-Effectiveness: It is typically more affordable than mobile shredding, making it a practical choice for large-scale IT cleanouts or routine equipment disposals.
- Operational Efficiency: The vendor manages all logistics, freeing up your team. You do not need to allocate space or personnel to supervise the process at your own facility.
- Scalability: A plant-based facility can process a massive number of drives much more quickly than a single mobile truck, making it ideal for large projects like data center decommissioning.
If you are weighing the benefits of having a mobile shred truck come directly to your business, especially for a high-security project, you can explore the details of professional on-site data destruction services. This will help you gain a deeper understanding of how these commercial services can be tailored to your specific requirements.
Why Chain of Custody and Certification Matter

When it comes to destroying sensitive corporate data, the job is not complete just because the hard drives have been shredded. It is only complete when you have the documentation to prove it. This is where chain of custody documentation becomes your most critical risk management tool.
Think of it as the unbroken, documented history of your hard drives, tracking them from the moment they leave your possession to the instant they are physically destroyed. A robust chain of custody ensures total accountability, leaving no gaps where an asset could be lost, misplaced, or stolen.
Without this documented trail, your business is operating blindly. You have no way to prove that every single asset was accounted for and destroyed, leaving your organization exposed to compliance fines and significant liability.
What an Ironclad Chain of Custody Involves
A truly secure process is not just about loading boxes onto a truck; it is a meticulous, transparent system designed for control and verification. This is what distinguishes professional, compliant secure destruction of hard drives from a high-risk gamble.
Here’s what a professional chain of custody looks like in practice for a business client:
- On-Site Asset Inventory: The process begins at your facility, where every hard drive's unique serial number is scanned and logged.
- Secure Transport: Drives are sealed in locked, tamper-evident containers before being moved in GPS-tracked, secure vehicles.
- Access-Controlled Facilities: The destruction facility must be a secure plant with strict access controls, 24/7 surveillance, and fully background-checked employees.
- Documented Handover: Every time the assets change hands—from your staff to the driver, and from the driver to the destruction technician—it is signed off on and documented.
This granular level of tracking provides a clear, auditable record that confirms every drive was handled securely from start to finish. It is precisely what auditors demand as proof of due diligence.
The Certificate of Destruction Explained
The final component is the Certificate of Destruction. This is not merely a receipt; it is a legally binding document that serves as your official proof that the job was completed correctly and that you have fulfilled your compliance obligations. It is your primary defense in an audit.
Your Certificate of Destruction is the legal document that formally transfers the liability for the destroyed data from your organization to your ITAD vendor. It certifies that you have met your data protection obligations.
For this certificate to be valid under scrutiny, it must be detailed. A vague, one-line certificate is a major red flag and will likely be rejected by auditors. Before you sign off, ensure it includes a serialized list of every asset, the exact destruction method used, the date and location of destruction, and an authorized signature.
To see a breakdown of a proper, audit-proof document, you can learn more about what makes a valid HDD destruction certificate. By demanding a rigorous chain of custody and a detailed certificate, you can confidently verify your vendor’s performance and ensure your compliance is fully documented.
Your Checklist for Selecting an ITAD Partner
Choosing the right IT Asset Disposition (ITAD) partner is one of the most critical decisions your business can make to protect its data. This is not simply about hiring someone to haul away old equipment. It is about entrusting a vendor with your most sensitive corporate information.
An excellent partner acts as an extension of your own security team, ensuring the secure destruction of hard drives is handled with precision, professionalism, and complete compliance.
Unfortunately, not all vendors operate with the same level of discipline. Using a detailed checklist to vet potential partners helps you look beyond marketing claims and focus on what truly matters: security, compliance, and accountability. This simple step ensures you find a true partner, not just a disposal service.
Verify Industry Certifications
Certifications are the fastest way to confirm a vendor's commitment to industry best practices. They are not just logos on a website; they are proof that the vendor has passed rigorous, third-party audits covering security, environmental responsibility, and safety.
Look for these key credentials for any commercial vendor:
- R2v3 (Responsible Recycling): A top-tier standard for electronics recycling, ensuring e-waste is managed in an environmentally sound and secure manner.
- e-Stewards: Similar to R2, this certification has a strong focus on preventing the illegal export of hazardous e-waste.
- NAID AAA Certification: This is the gold standard specifically for data destruction companies. It verifies secure processes for shredding, sanitization, and chain of custody, and it requires that all employees handling sensitive material pass strict background checks and security training.
A vendor holding these certifications has already invested significant time and resources to prove they meet the highest operational standards in the commercial sector.
Review Security and Reporting Capabilities
Beyond certifications, you must examine the details of a vendor's process. A professional ITAD partner should provide transparent and detailed documentation for every step of the service.
The right ITAD partner provides more than just a service; they provide proof. Detailed, serialized reporting is your evidence of due diligence and your best defense in a compliance audit.
Ask potential vendors about their specific procedures for serial number tracking and reporting. Can they provide a serialized inventory of every single asset they process? This level of detail is critical for your own records and for proving compliance. It is also wise to consult a detailed guide, and you can start with this vendor due diligence checklist to ensure you cover all necessary bases for your business.
Confirm Insurance and Value Recovery
Finally, assess the vendor's business practices. Confirm they carry adequate liability insurance, including a specific policy for data breach protection. This coverage protects your organization in the highly unlikely event that something goes wrong.
You should also inquire about their value recovery program. Can they test and resell viable corporate assets? This could provide a potential return on your retired equipment, turning a cost center into a potential revenue stream for your business.
The demand for these secure services is driving significant market growth. The global Hard Disk Destruction Equipment Market was valued at USD 2.85 billion in 2025 and is projected to reach USD 4.23 billion by 2032. This growth underscores the increasing global focus on using certified equipment for data destruction. You can read the full research about hard disk destruction equipment.
Frequently Asked Questions About Hard Drive Destruction
Even with a robust plan, it is natural for businesses to have questions regarding the secure destruction of hard drives. This section addresses the most common queries from business owners and IT managers, providing clear answers to help you proceed with confidence.
Can I Just Drill Holes in My Hard Drives?
Drilling holes in a hard drive might seem like an easy and effective DIY destruction method, but it is dangerously unreliable for a business. While you will certainly damage the drive's platters, you often leave large sections of the data-storing surfaces perfectly intact.
A determined data thief with forensic recovery tools can often retrieve significant information from drives that were only drilled or hammered. For true business-grade security and regulatory compliance, physical shredding or degaussing are the only methods that guarantee data is completely and permanently unrecoverable.
Wiping vs Shredding for Compliance
The best method depends on your specific regulatory requirements and whether you want to reuse the hardware to recover value for your business.
- Data Wiping (Sanitization): A software-based approach that overwrites all data, leaving the hardware intact for reuse or resale. It is fully compliant with standards like NIST 800-88 "Purge" and is the ideal choice for corporate assets you plan to resell for value recovery.
- Shredding (Destruction): Physically destroys the drive, making data recovery impossible. It aligns with the highest level of compliance for regulations like HIPAA and DoD requirements, where total media destruction is often preferred or mandated for business assets.
For organizations in high-stakes industries like healthcare or finance, shredding offers absolute certainty and is often the simplest path to proving compliance. Data wiping is a secure alternative when asset reuse is a business priority.
What Happens to the Shredded Material?
After your business's hard drives are pulverized into tiny fragments, the material is not sent to a landfill. As a certified electronics recycling provider, Beyond Surplus ensures the shredded remains enter a responsible downstream recycling process.
The mixed metals, including aluminum, steel, and trace precious metals, are sorted and sent to specialized smelters. There, they are melted down and refined for use in manufacturing new products. This closed-loop system ensures your data is permanently destroyed while adhering to strict environmental standards.
How Much Does Secure Hard Drive Destruction Cost?
The cost of professional hard drive destruction for businesses varies, as there is no single flat rate. Each project's unique factors influence the final price.
Key cost drivers for commercial services include:
- Service Type: On-site mobile shredding typically costs more due to the logistics and security of bringing a shred truck to your facility. Off-site, plant-based shredding is generally the more cost-effective option for businesses.
- Volume: The price per drive almost always decreases as the quantity of drives increases.
- Location: Your business's physical location, logistics, and travel time can all influence the total project cost.
The only way to get a precise number is to request a custom quote based on your specific inventory and service needs.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal. We provide compliant and documented secure destruction of hard drives for businesses across the United States.