You search e-waste recycle near me because a storage room is full, the office is moving, or a refresh cycle just ended. What looks like a disposal task is usually a security and compliance project in disguise.
For a business, old laptops, servers, phones, network gear, and retired medical or lab equipment aren't just scrap. They hold regulated data, licensed software, asset tags, and chain-of-custody obligations. If those items leave your control without documented handling, the risk doesn't disappear with the hardware.
Beyond the Search Bar The Business Risks of E-Waste
Most search results for e-waste recycle near me are built for household drop-offs. That's the wrong frame for an IT manager, facilities lead, or procurement team trying to retire company equipment. A consumer program may accept devices, but acceptance isn't the same as compliant processing.

The scale of the problem matters. Global e-waste is projected to reach 82 million tonnes by 2030, an 82% surge from 2010, and that volume would fill 1.55 million 40-tonne trucks, enough to form a line around the equator, according to global e-waste statistics compiled by EMEW. Businesses contribute to that stream every time they replace endpoints, retire storage arrays, or decommission a data room.
What local recycling searches usually miss
A map result rarely tells you the things that matter most to a business:
- Data handling: Was the drive wiped to a recognized standard or just collected?
- Asset traceability: Can the vendor report every serial number from pickup through final processing?
- Downstream control: Do they know where boards, batteries, plastics, and drives go?
- Liability transfer: Will you receive documentation that stands up in an audit?
Practical rule: If the provider can't explain chain-of-custody before pickup, they're a recycling outlet, not an ITAD partner.
ITAD is the business standard
IT asset disposition, or ITAD, treats retirement as a controlled operational process. It starts with inventory and custody, then moves through data destruction, value recovery where appropriate, and documented recycling. That's very different from dropping mixed electronics at a public collection point.
Business teams usually need a partner that can support secure pickups, serialized reporting, and policy-aligned processing for multiple asset classes. That's why many organizations start with a dedicated business e-waste recycling program instead of relying on generic local options.
When you're evaluating disposal options, don't ask only, "Who is close?" Ask, "Who can prove what happened to each asset after it left our floor?"
Finding a Certified Recycler Not Just a Local Drop-Off
Distance matters less than controls. A nearby scrap hauler may be convenient, but convenience doesn't help if legal, privacy, or procurement teams later ask for destruction records and downstream documentation.

When benchmarking e-waste partners, prioritize NAID AAA certification for 99.99% destruction efficacy and R2/ISO certification, which reduces non-compliance risk by 95%. Leading Atlanta firms like Beyond Surplus achieve near-100% compliance with these standards, according to First America's e-waste benchmarking overview.
Certifications that change the risk profile
A business recycler should be able to discuss certifications in plain language, not just paste logos onto a quote.
- R2 and ISO-related process controls: These indicate structured handling, tracking, and environmental accountability.
- NAID AAA: This matters when physical destruction is part of scope, especially for storage media.
- Audited downstream practices: Certifications are stronger when the vendor can explain how they monitor where materials go next.
If you need a plain-English primer, R2 certification for electronics recycling is worth reviewing before vendor interviews.
Questions worth asking on the first call
Use the first conversation to surface gaps fast.
- How do you document chain-of-custody? Ask whether assets are serialized at pickup or after arrival.
- What destruction methods do you offer? A credible vendor should explain wiping versus shredding without hand-waving.
- What reports do we receive? You want asset-level reporting, not a generic weight ticket.
- Do you support on-site services? This is important for higher-risk environments.
- How do you handle reuse versus destruction? Good ITAD programs separate recoverable devices from end-of-life scrap under controlled rules.
A recycler that talks only about tonnage and haul-away speed is telling you how they move material, not how they protect your business.
Red flags that should stop the process
Some warning signs are immediate:
- No clear answer on certificates
- No discussion of insurance or indemnification
- No asset-level tracking
- No explanation of downstream vendors
- Pressure to skip inventory because it "slows things down"
A real ITAD partner knows that speed without documentation creates expensive cleanup later.
Preparing Your IT Assets for Secure Disposal
The strongest recycling project starts before pickup day. Internal preparation determines whether you can reconcile assets later, separate reusable hardware from destruction candidates, and show that your team handled retirement under policy.

A staggering 1 in 10 devices still contain recoverable data after user "wiping". Professional data destruction, using either NIST 800-88 sanitization or physical shredding to <2mm particles, is the only way to ensure 99.9%+ data security and avoid liability, according to Atlanta Computer Recycling's ITAD process summary.
Build the asset list first
Before anything leaves the building, create a serialized inventory. Include whatever your organization already tracks, such as make, model, serial number, asset tag, location, assigned department, and disposition path.
That list does three jobs at once:
- Operational control: Your team knows what should be picked up.
- Security control: Data-bearing assets are visible before transport.
- Audit support: The final report can be reconciled against your internal list.
Decide between wiping and shredding
Not every device should follow the same path.
Certified wiping under NIST 800-88 is usually appropriate when the device may be reused, remarketed, or donated after sanitation. Physical shredding is the better choice when policy, sensitivity, contract requirements, or device condition make reuse unacceptable.
A practical split often looks like this:
- Laptops in usable condition: sanitize, test, then evaluate for reuse or resale
- Failed drives and damaged storage media: shred
- Servers from regulated environments: often shred drives first, then process remaining hardware
- Mixed pallets from office cleanouts: separate data-bearing assets before general loading
Teams that need drive destruction as a standalone control should review secure hard drive destruction options before scheduling.
Treat "we factory-reset everything" as a starting point, not a final control.
Prepare assets for pickup day
A clean handoff prevents errors. Tag pallets or carts by disposition category, keep loose drives separate from non-data peripherals, and make one person responsible for sign-off when the carrier arrives. If your company uses DBAN, Blancco, or similar wiping tools internally, document that activity but still require independent reporting from the ITAD vendor.
The best projects aren't complicated. They're controlled.
Choosing Your Logistics Model Pickup Drop-Off or Mail-In
Logistics should match risk, volume, and internal labor capacity. The wrong transport model creates delays, custody gaps, and unnecessary handling.
Business E-Waste Logistics Models Compared
| Service Model | Best For | Security Level | Key Benefit |
|---|---|---|---|
| Pickup | Office refreshes, data center work, multi-pallet loads | High when paired with chain-of-custody and scheduled handoff | Minimal internal transport burden |
| Drop-off | Smaller local business loads with staff available to deliver | Moderate to high if intake is documented properly | Fast local turnaround |
| Mail-in | Remote sites, small batches of select assets, distributed teams | Varies by packaging and tracking controls | Useful for hard-to-reach locations |
When pickup is the right call
Pickup works best when you have enough equipment that internal transport becomes its own project. It's also the practical choice for server racks, storage arrays, network closets, and decommissioning events where timing matters.
For organizations managing larger or recurring retirements, a scheduled IT equipment pickup service usually gives better custody control than sending staff to a public drop site.
When drop-off still works
Drop-off can be efficient for local companies with a small batch of retired laptops, monitors, docks, and peripherals. It works best when your staff has already built the asset list and the receiving facility provides documented intake.
The mistake is assuming drop-off means informal handling. For a business, even a small load still needs check-in discipline.
Where mail-in fits
Mail-in programs are useful for branch offices, remote workers, and specialty returns where pickup would be inefficient. They work best for compact, high-value assets rather than mixed scrap.
Choose the model that reduces touches. Every extra handoff is another place where serial numbers, custody, or hardware condition can drift.
If data sensitivity is high, ask whether on-site shredding should happen before anything moves.
The Final Step Certificates for Compliance and Liability Transfer
For a business, the truck leaving isn't the finish line. The ultimate deliverable is paperwork that proves what happened.
Free municipal e-waste programs often lack the necessary documentation for business compliance, exposing companies to potential data breach fines exceeding $1M under FTC rules. Certified ITAD firms provide Certificates of Destruction that transfer this liability, as noted in Monroe County's electronics recycling context and business-risk discussion.
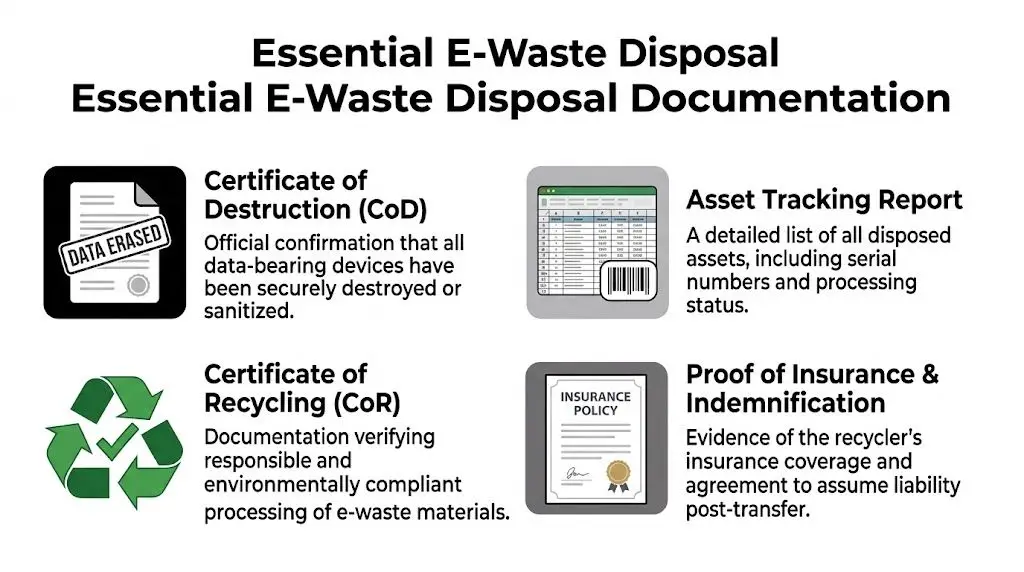
The documents that matter
You should expect more than a receipt.
- Certificate of Destruction for data-bearing devices processed through wiping or shredding
- Asset tracking report showing serial numbers and disposition status
- Certificate of Recycling confirming responsible processing
- Insurance and liability documentation when required by legal or procurement
A proper certificate of destruction process is what separates defensible disposal from hopeful disposal.
Why certificates matter to auditors and legal teams
These records support retention, privacy, and disposal policies. They also help when compliance teams ask how retired hardware was handled, or when ESG reporting requires documented evidence of responsible processing.
Without those records, your organization is left with an assumption: that the recycler did what they said. That's not enough in healthcare, finance, government, or any environment where device retirement intersects with regulated information.
If a vendor can't produce serialized documentation, they haven't completed the business part of the job.
Documentation is where liability transfer becomes real. Until then, the risk still points back to you.
Frequently Asked Questions for Business E-Waste Recycling
Do businesses need more than a recycling receipt
Yes. A weight ticket or generic receipt doesn't identify which devices were processed. Business disposal should produce asset-level documentation tied to your inventory and destruction or recycling outcomes. That's what makes the project auditable.
Should every hard drive be shredded
Not always. If equipment is a candidate for reuse or remarketing, certified sanitization may be the right path. If the drive is failed, heavily regulated, or covered by strict internal policy, shredding is often cleaner from a risk standpoint. The decision should come from your data classification rules, not convenience.
Can a recycler help recover value from retired equipment
Yes, if the hardware is still viable and your policy allows reuse after secure sanitization. That usually applies to newer laptops, desktops, phones, and some network gear. Equipment that's obsolete, damaged, or nonfunctional is typically better routed directly to recycling and material recovery.
What about data center decommissioning projects
Those projects need more coordination than standard office pickups. Servers, drives, rails, switches, UPS units, and rack hardware should be inventoried in groups, with clear labeling for reuse, resale, or destruction. Chain-of-custody becomes more important as the number of assets rises.
How should healthcare, finance, and labs approach disposal
They should assume disposal is a controlled compliance event. That means stricter internal inventory, tighter release approval, and a documented destruction or sanitization standard. Devices used in clinical, payment, research, or public-sector environments deserve less improvisation and more written procedure.
Is a local recycler always the best option for e-waste recycle near me
Not for commercial work. Local is helpful only if the provider can meet the same custody, destruction, and reporting standards you'd expect from a national ITAD project. Many businesses do better with a regional or nationwide partner that can align service across offices and provide consistent documentation.
Contact Beyond Surplus for certified electronics recycling, secure IT asset disposition, and documented data destruction for business equipment across the United States.